- 05 Feb 2026
- 3 Minutes to read
- Print
- DarkLight
- PDF
What is a service principal?
- Updated on 05 Feb 2026
- 3 Minutes to read
- Print
- DarkLight
- PDF
Introduction
Service principal is an application within Microsoft Entra ID, which is authorized to access resources in Azure. This access is restricted by the roles assigned to the service principal, giving you control over which resources can be accessed and at which level.
Turbo360 leverages the authentication tokens of the service principal to manage resources by associating the azure service principal with the required permissions. These permissions are restricted to exactly what Turbo360 can do.
The necessary activities to perform such restrictions include:
- Create a service principal.
- Authorize and Assign a role to the service principal.
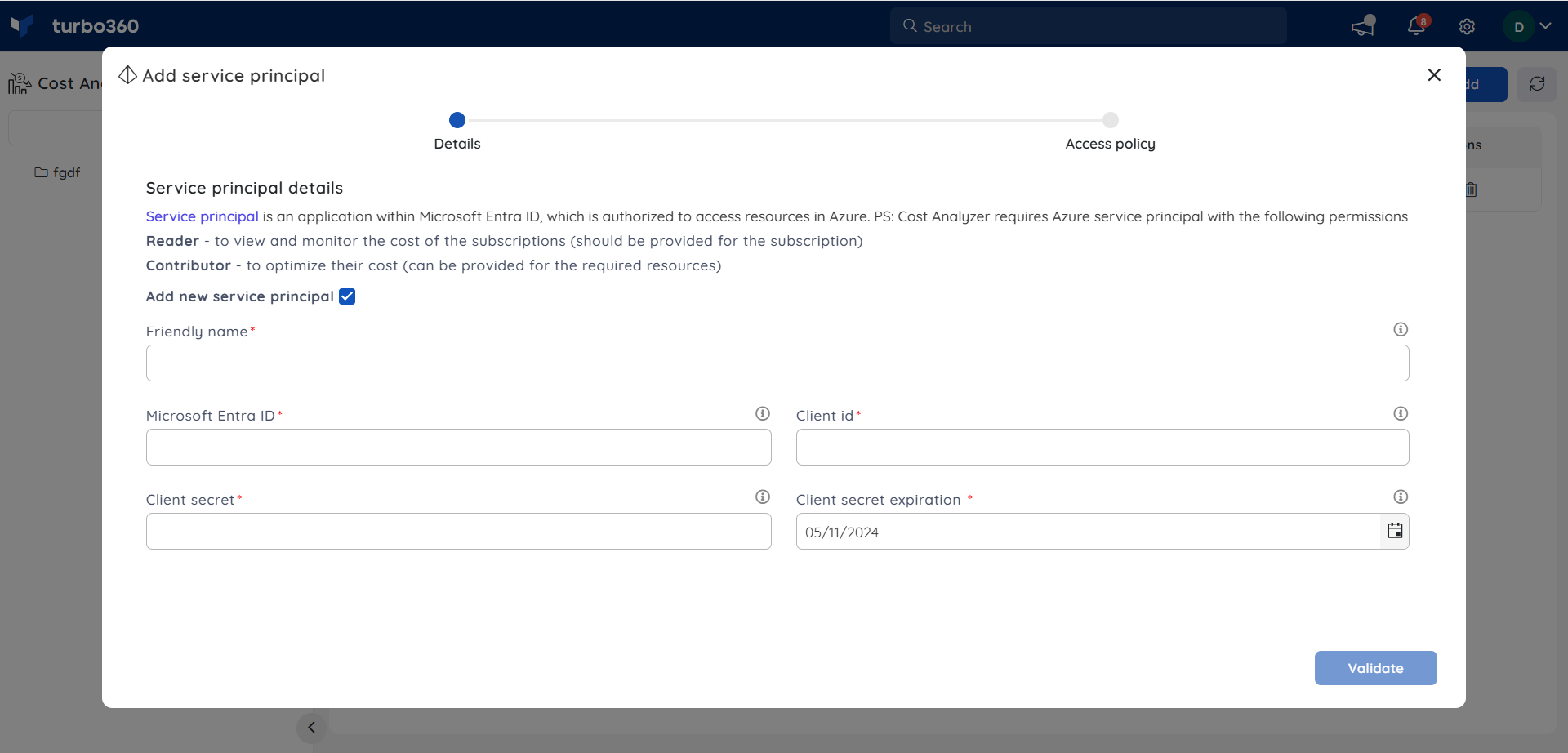
To associate a Service Principal with Turbo360, the following values are required:
- Microsoft Entra ID - Tenant directory Id.
- Client Id - Id of the service principal object / App registered with the Microsoft Entra ID.
- Client Secret - Application password.
Why does Turbo360 needs reader access for the service principal?
To access the user's azure subscription cost, the service principal must have Reader access at the Subscription level. Without this permission, users won't be able to view their subscription's cost.
Reservation Reader access must be provided to the service principal to view reservations and reservation-based recommendations.
Create a service principal
To create a service principal, perform the following steps:
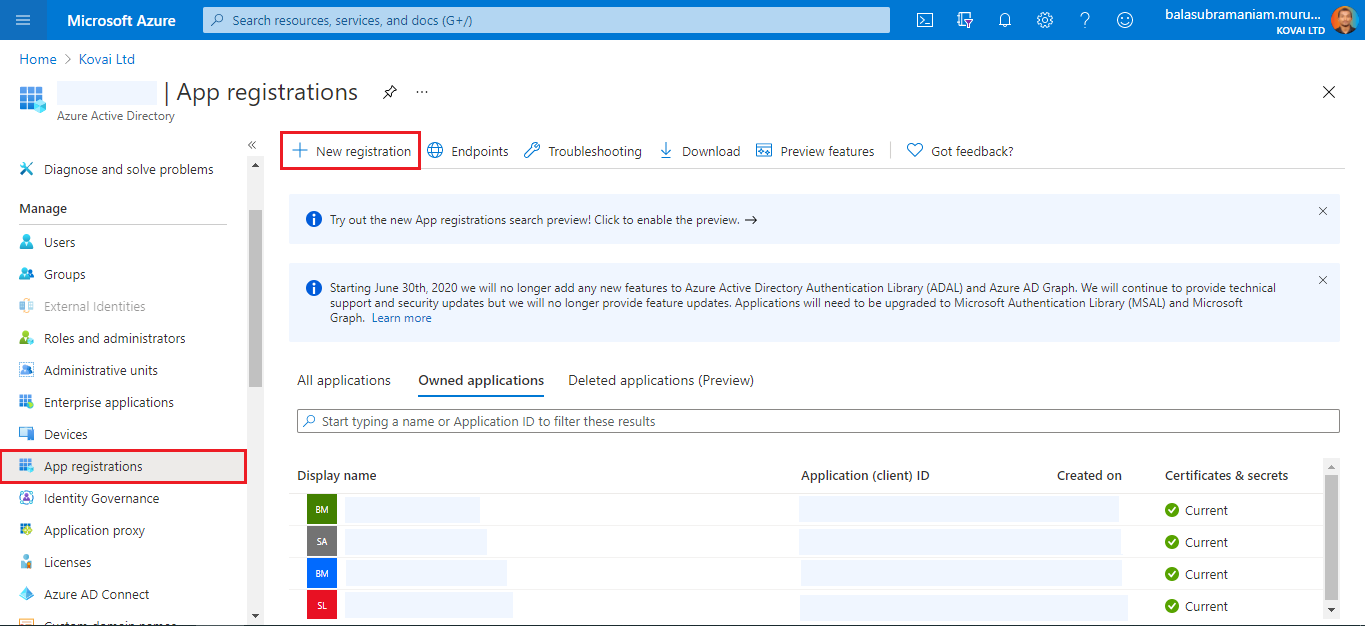
Navigate to the Microsoft Entra ID tab in the left side menu in the azure portal and click App registrations.
Click on the New registration button.
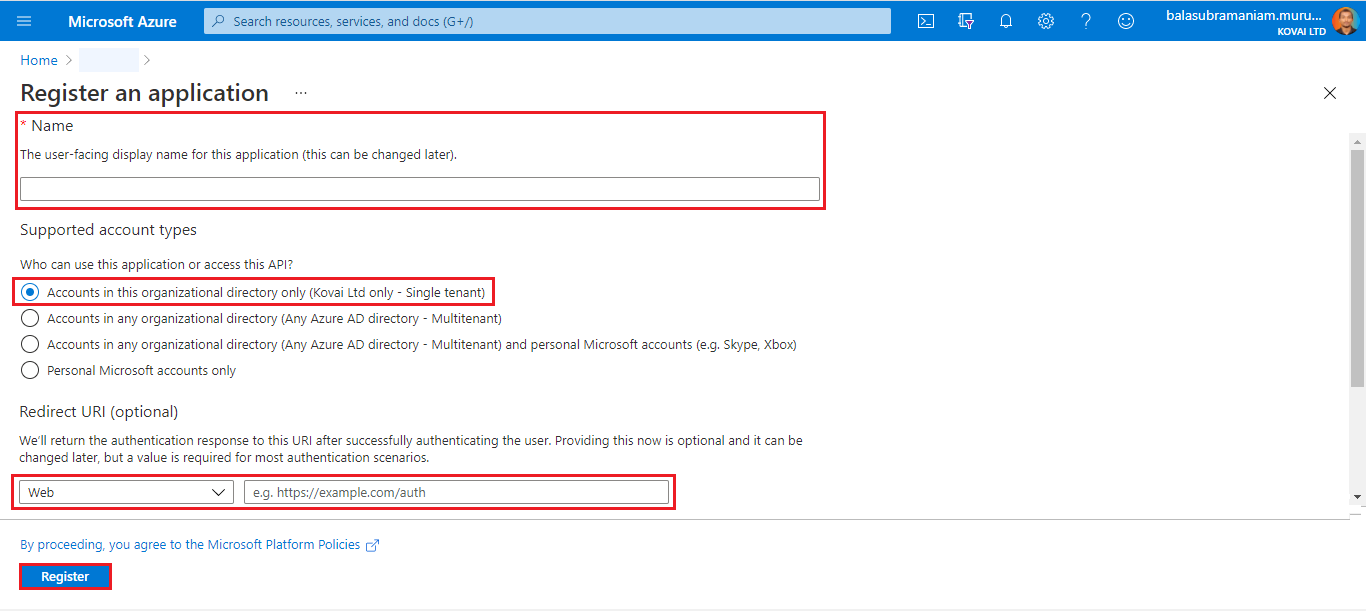
Provide a Name for the service principal. Select a supported account type, which determines who can use the application. Under Redirect URI, select Web for the type of application that needs to be created. Enter the URI to which the access token is sent to. Click on the Register button.
Once the service principal is created successfully, it will be listed in the App Registration grid.
Get Azure Tenant ID
In Azure Microsoft Entra ID, a tenant is a representative of an organization.
It is a dedicated instance of the Azure Microsoft Entra ID service that an organization receives and owns when it creates by signing up for a Microsoft Azure account.
Each Azure AD tenant is distinct and separate from other Azure Microsoft Entra ID tenants.
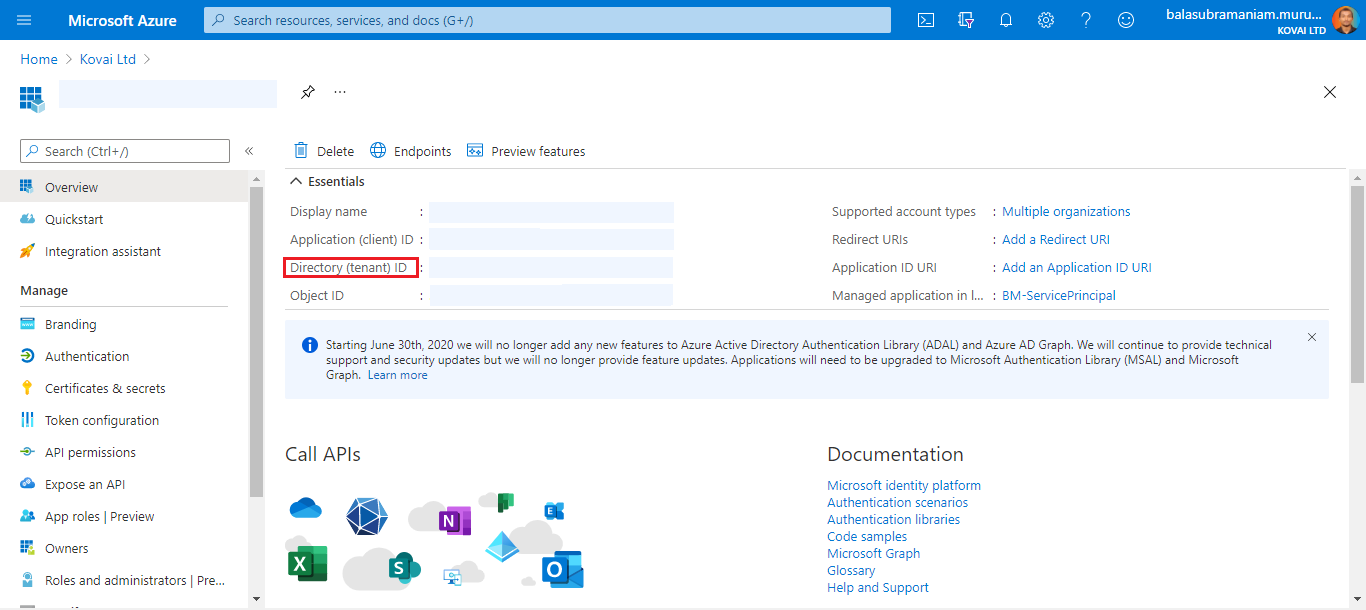
In order to obtain the Tenant ID, perform the following steps:
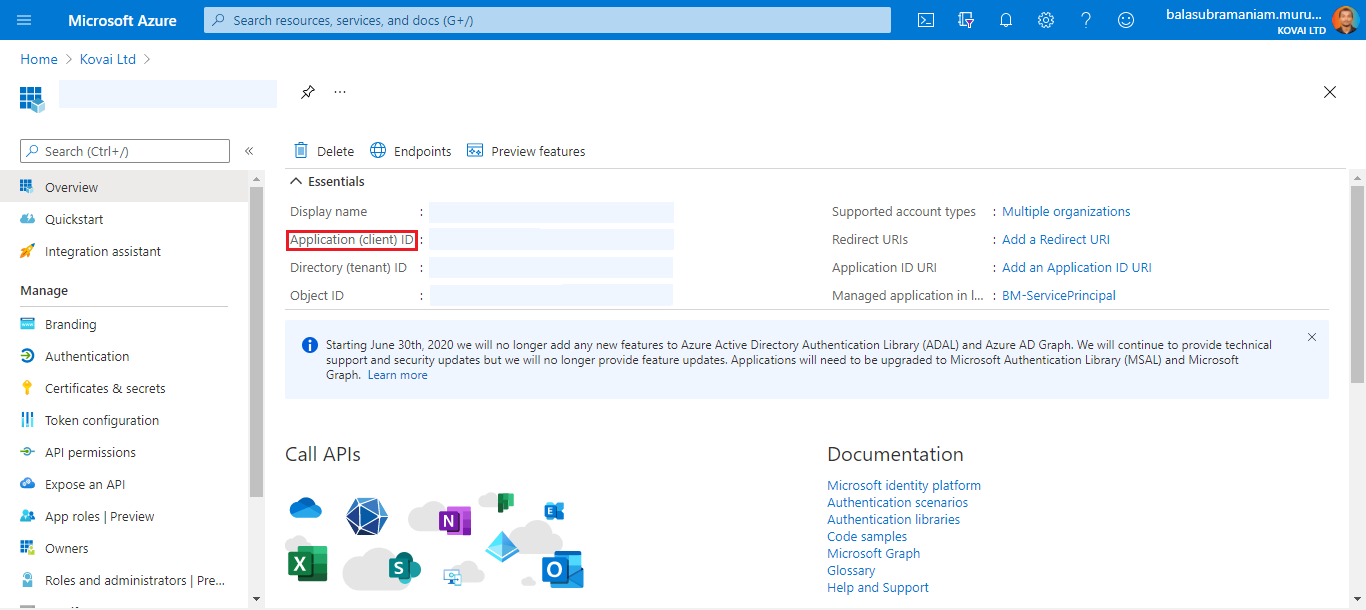
Click on the name of the service principal.
The required Tenant Id is the Directory (tenant) ID from the Essentials section.
Get Client ID and Client Secret
A Client ID is a 16-character string that represents the application.
Follow the below steps to obtain the Client ID:
Click on the name of the service principal.
The required Client Id is the Application (client) ID from the Essentials section.
Secret key is a security key that Windows Live ID uses to encrypt and sign all tokens. It is used by the application to prove its identity when requesting a token.
To obtain the Client secret, follow the below steps:
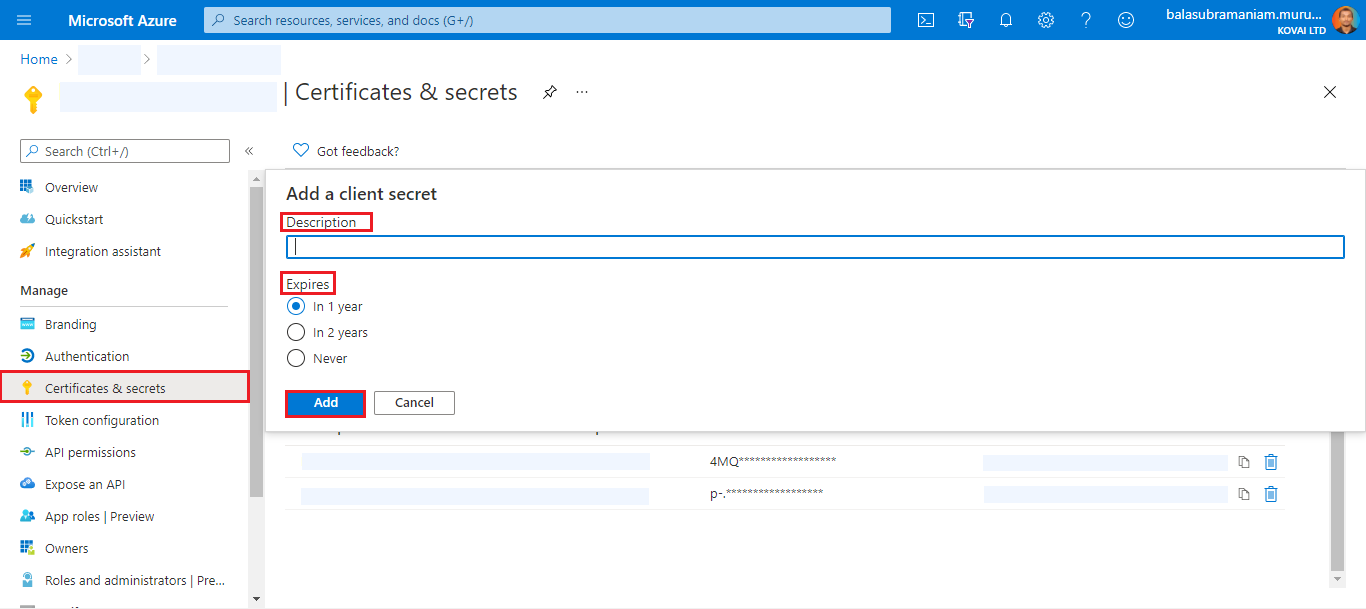
Click on Certificates & secrets under the Manage section from the left pane.
Click on New client secret, provide the Description and Expiry time, and Click Add.
Once saved, it will show the client secret. This key will only be shown once. This value should be copied and saved.
Authorize service principal and role assignment
To access the resources in a subscription, the application must be assigned to a role. The right permissions for each role are defined based on different use cases. The scope of the application can be set at the level of the subscription, resource group, or resource.
Permissions are inherited to lower levels of scope. For example, if an application has the Contributor / Owner role for a resource group, it can access the resource group and any resources it contains.
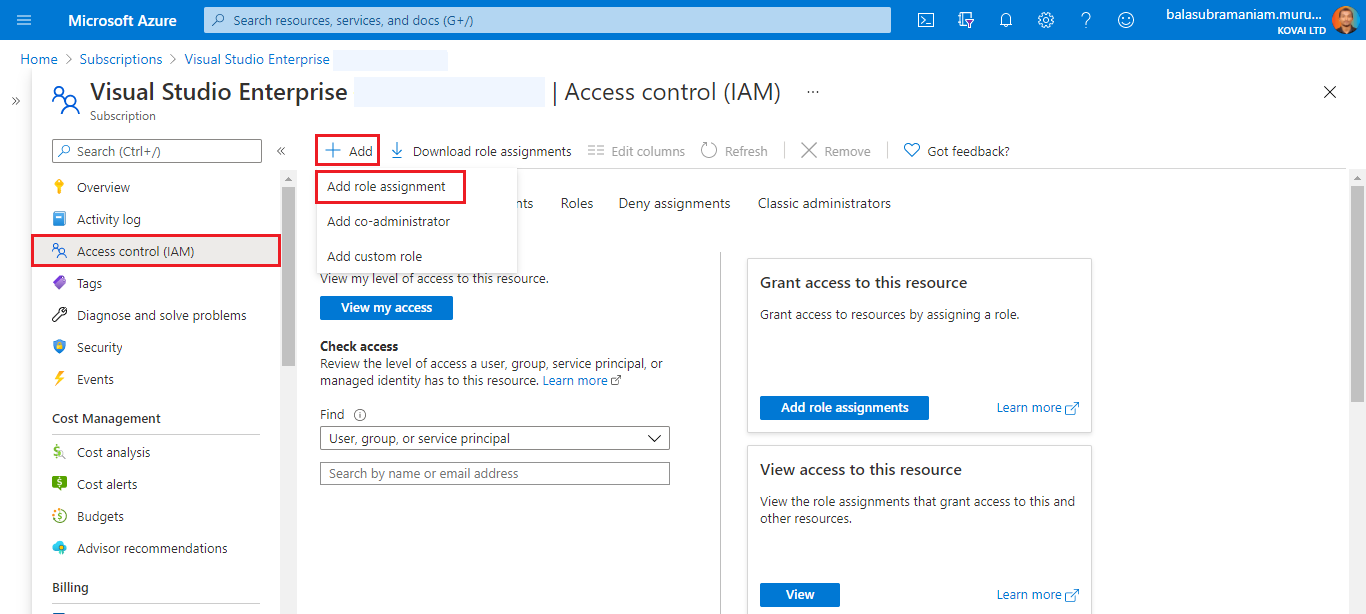
To authorize the service principal to access a Subscription:
Navigate to that Subscription. Click on Access control (IAM).
Select Add->Add role assignment.
- Switch to the Job function roles tab and choose Reader.
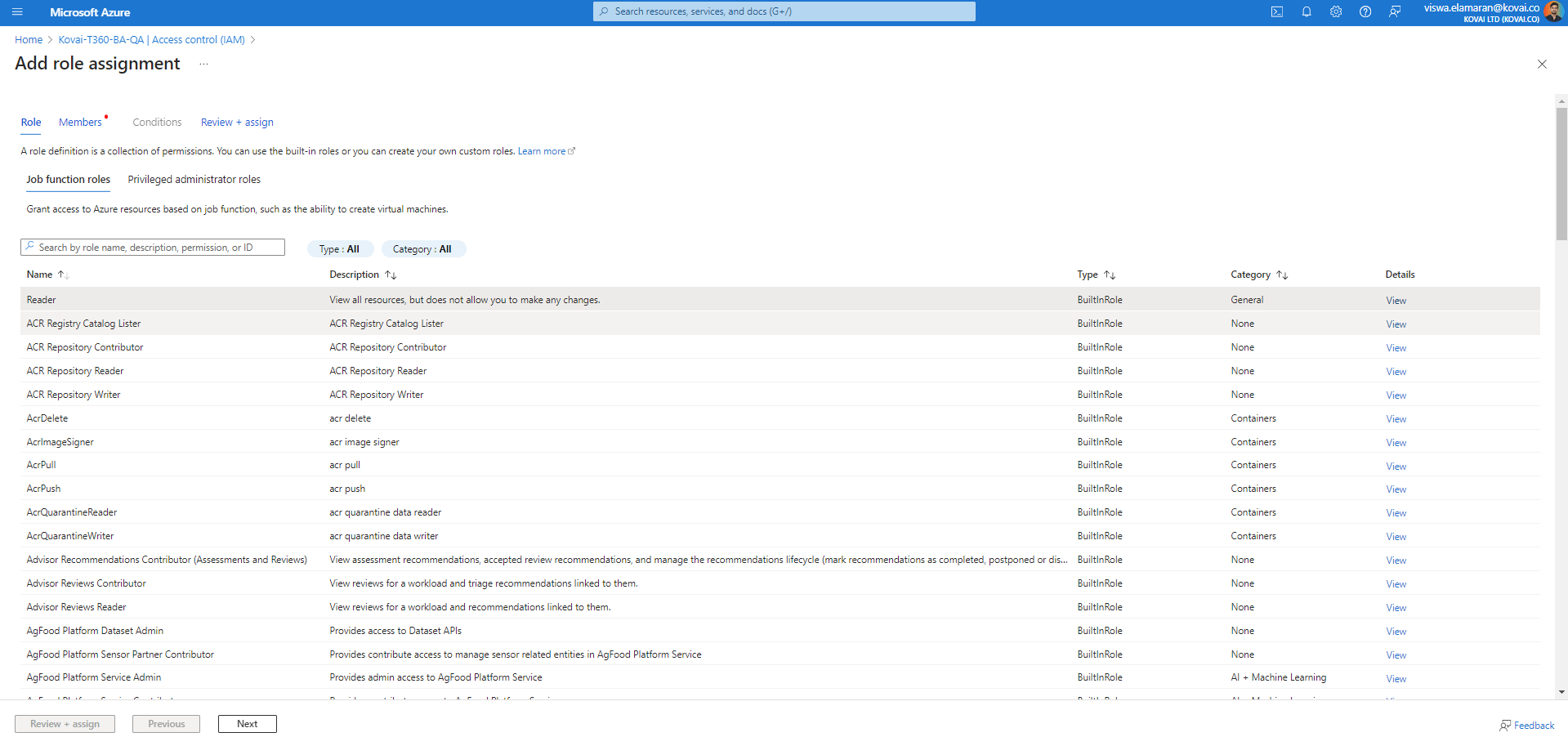
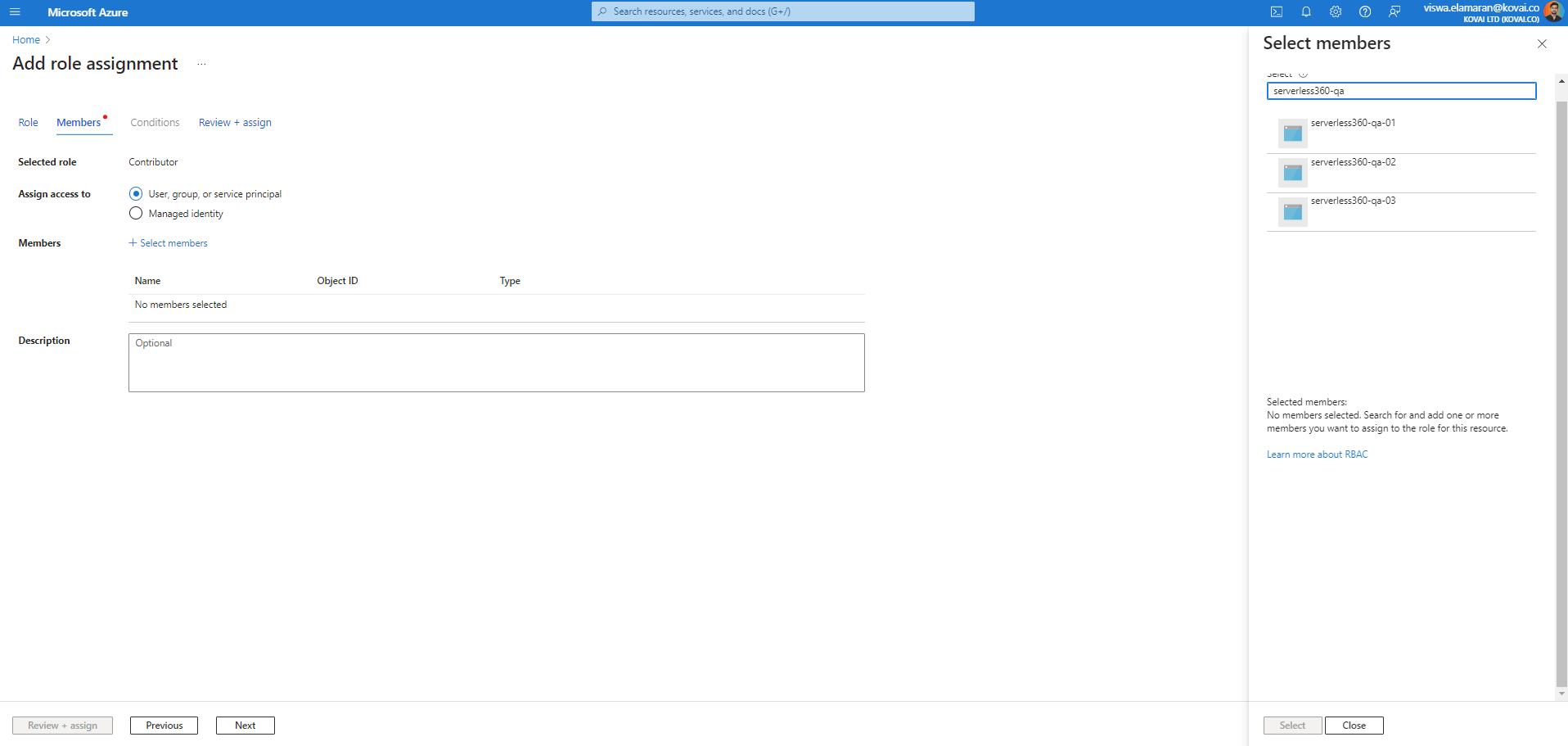
Clicking Next will proceed to the role assignment screen. Choose User, group, or service principal option for the Assign access to field.
Multiple service principals can be assigned with the specified role acess for the relevant Azure Subscription by selecting them as its Members.
Click Review+assign to review and save the role assignment.
It may take some time for the above configurations to take effect.
To know more about service principals and the above process, read the following articles from Microsoft:

